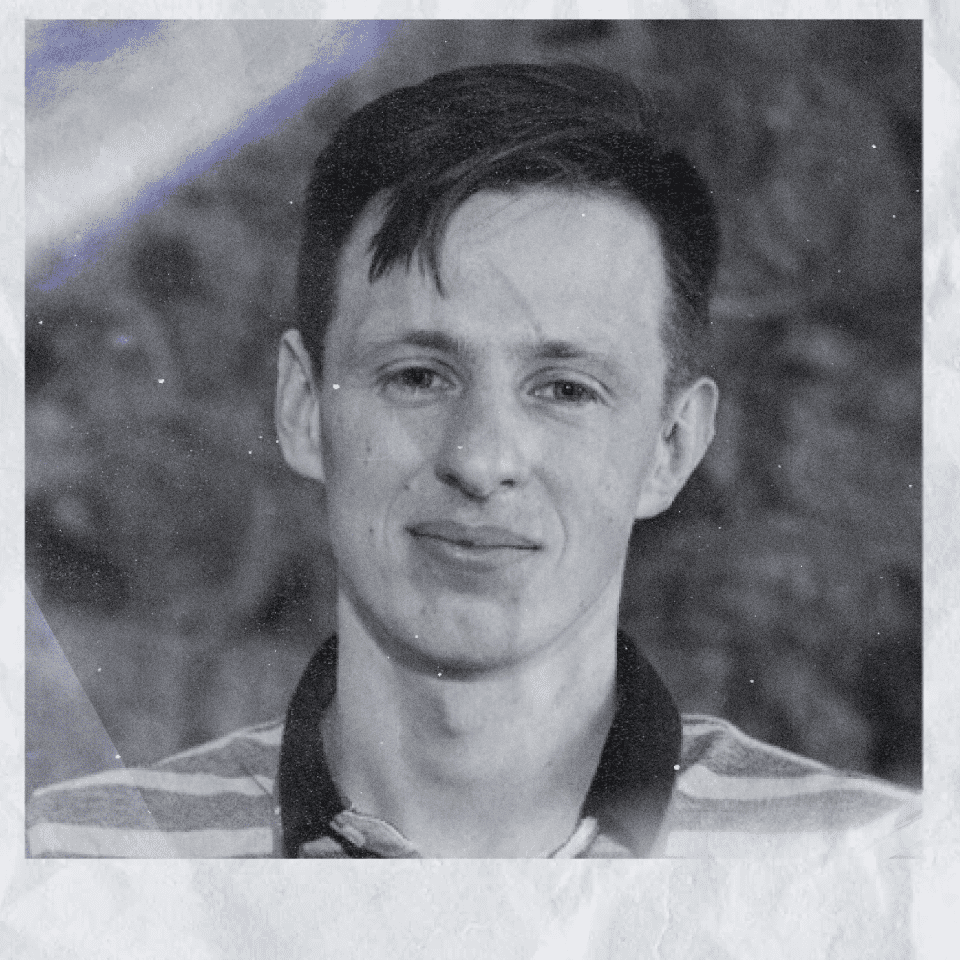
Eugene Rodionov
Launch Secured: A Story on Red Teaming the Pixel 6
Despite the large number of phone vendors, most Android devices are based on a relatively small subset of system on a chip (SoC) vendors. Google decided to break this pattern with the Pixel 6. From a security perspective, this meant rather than using code that had been tested and used for years, there was a new stack of high value device firmware we needed to get right the first time.
This presentation will showcase the value of red teaming by demonstrating results of offensive testing of Pixel 6 before its release to ensure a more secure and safe launch of the product. The authors will deep dive into methodology and tools used to proactively mitigate attack surface exposed by new and updated firmware components in Pixel 6. They will demonstrate privileged code execution in critical components such as: the updated Titan M2 chip, and Android bootloader with full persistence. To conclude the presentation authors will discuss the impact of the proactively identified issues for Android platform security and reflect on the prevented potential attacks scenarios.
Eugene Rodionov, PhD, is a Security Researcher at Google on the Android Red Team. In his current position, Eugene focuses on finding and exploiting vulnerabilities in the low-level components of Android platform and Pixel devices. Prior to that, Rodionov performed offensive security research on UEFI firmware for Client Platforms at Intel, and ran internal research projects and performed in-depth analysis of complex threats at ESET. His fields of interest include reverse engineering, vulnerability analysis, firmware security and anti-rootkit technologies. Rodionov is a co-author of the “Rootkits and Bootkits: Reversing Modern Malware and Next Generation Threats” book and has spoken at security conferences such as Black Hat, Ekoparty, REcon and ZeroNights.